
Vulnerability Assessment & Penetration Testing (VAPT)
VAPT OVERVIEW
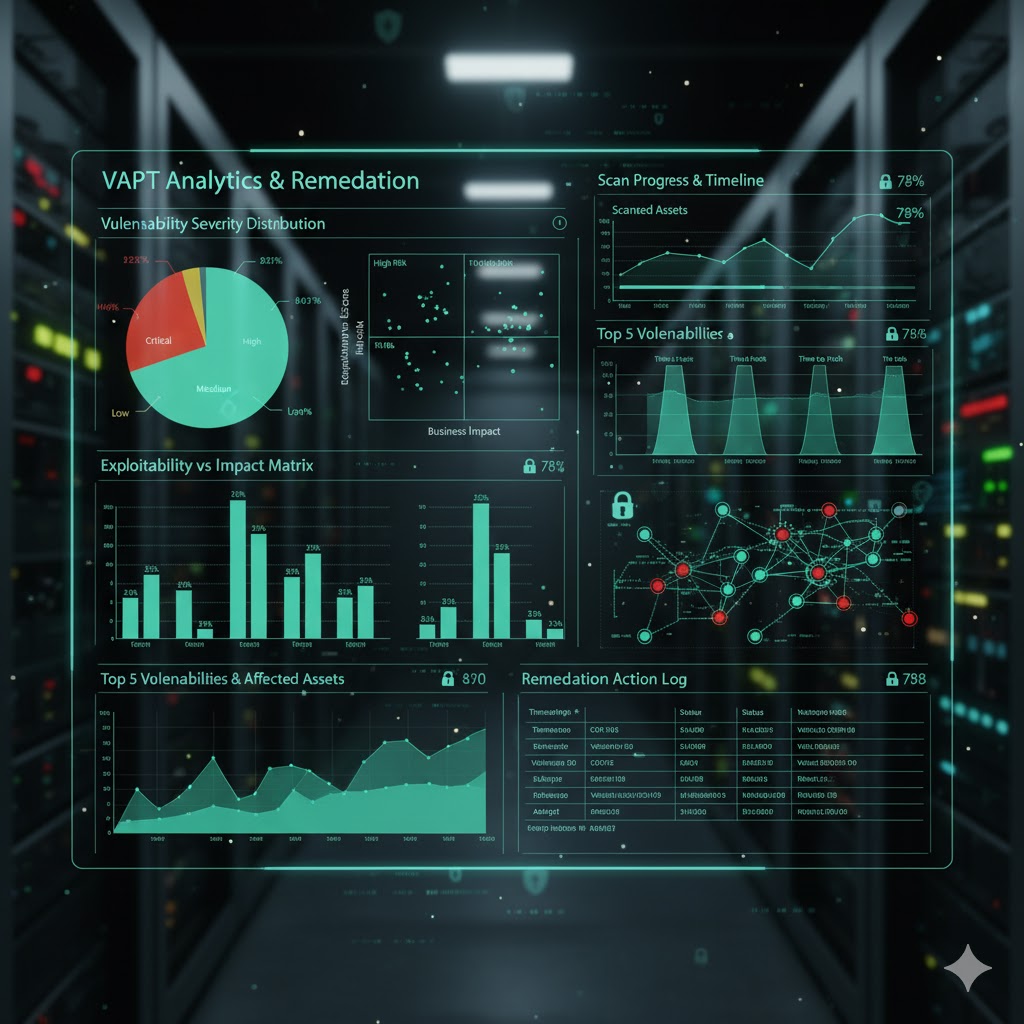
As organizations grow increasingly dependent on ICT infrastructure, risk of unauthorized access and security breaches rises, so it's essential to assess applications, networks, and systems for vulnerabilities and to use rigorous testing that simulates how an attacker would gain entry and move laterally; because new applications and infrastructure changes continuously introduce fresh weaknesses, frequent security assessments are crucial .
Our Security Assessment Services exploit those vulnerabilities in controlled, safe conditions to determine what information is exposed, mimic real attacker techniques without placing the organization in actual jeopardy, and provide clear findings so teams can remediate each weakness effectively.
ASSESSMENT SERVICES
Comprehensive testing approaches to identify vulnerabilities

Black-box Testing
Emulating an External Attacker
Black-box Testing
Simulates real-world attack scenarios by testing from an external perspective with no prior knowledge of internal systems, mimicking how actual attackers would approach your infrastructure.

Grey-box Testing
Emulating Legitimate Users
Grey-box Testing
Combines internal and external testing perspectives with limited system knowledge, simulating insider threats and authenticated user access to identify privilege escalation vulnerabilities.
White-box Testing
Analysis with Full Access
White-box Testing
Comprehensive analysis with complete access to source code, architecture, and documentation, enabling thorough examination of internal security mechanisms and code-level vulnerabilities.
OUR SERVICES DETAILS
Application Security Assessment
- •Web Application Assessment
- •Android Application Assessment
- •iOS Application Assessment
- •Desktop/Legacy Application Assessment
Network Infrastructure Security Assessment
- •External Security Assessment of Network Devices
- •Internal Security Assessment of Network Devices
- •Security Configuration Audit
Database Security Assessment
- •Database Configuration Audit
- •SQL Injection Tests
- •Insecure Storage Evaluation
- •Password Policy Evaluation
- •Permissions Evaluation